With so many publishers large and small running on the WordPress platform it is a natural target for hackers. The overall security of your site depends on a lot of factors, including the security protocol your hosting company implements at the server level. Some hosts are more secure than others. You should investigate your host for yourself.
Don't take their, "we take the security of your site very seriously" corporate nonsense at face value. If lots of people complain about their sites being hacked and the common denominator is their host, well - that pretty much speaks for itself.
That said, there's a lot you can do to help to protect your site from hacking attempts by malicious douchebags. Here are a handful of things I believe anyone running WordPress should do to help better secure a site and reduce the chances of it being hacked (or, at the very least, make it more difficult to hack).
Installing WordPress
 If at all possible DO NOT use a tool like Fantastico or Softaculous (both of which are often provided by your hosting service to streamline the installation process).
If at all possible DO NOT use a tool like Fantastico or Softaculous (both of which are often provided by your hosting service to streamline the installation process).
While those tools make installation SUPER easy, their cookie-cutter installation settings can also make WordPress installations more vulnerable.
The software is easy to install manually by following the simple installation instructions in the WordPress Codex.
If you can't follow those simple instructions you probably should not be doing any of this on your own to begin with.
Always Create a New Database
 If your host provides cPanel access creating a new database is very easy. Use a little common sense when naming your database (i.e. don't name it "wordpress", "wrdp", etc.) Create a name you will be able to remember is associated with that particular website, but something a hacker or automated attack program wouldn't easily identify with a specific domain. For example, the database name for www.domain.com should not be "domain". You can use both letters and numbers in the database name. And I suggest you do.
If your host provides cPanel access creating a new database is very easy. Use a little common sense when naming your database (i.e. don't name it "wordpress", "wrdp", etc.) Create a name you will be able to remember is associated with that particular website, but something a hacker or automated attack program wouldn't easily identify with a specific domain. For example, the database name for www.domain.com should not be "domain". You can use both letters and numbers in the database name. And I suggest you do.
Once your new database has been created you will need to assign a database user to it. You should always create a new user for each database. Using the same user for every database is asking for trouble. In the event that someone gains access to your hosting space they could potentially gain access to every database that exists there using the same user information. That would be bad. As with naming the database, use some common sense. The username shouldn't match your domain or your database name. Again, you can use both letters and numbers. And again, I suggest you do.
You will also have to assign a password to your new database user. I use the password generator from Strong Password Generator. The tool offers two recommended password lengths, 7 and 14. Never use recommended password lengths. Why? Because most people do. And when it comes to securing your WordPress installation, the last thing you want to do is what most people do. Choose another password length. The longer, the better. The database user password can contain letters, numbers and symbols. For the best security, make sure it contains all three.
Editing Your wp-config.php file
 Now that you've created your new database and database user (I sure hope you kept copies of the names and password, because you'll need them now), it's time to make some changes to your wp-config.php file. NOTE: when you upload WordPress the name of that file will be wp-config-sample.php. Follow the instructions for making the necessary changes to the file in the "WordPress Famous 5-minute Install" and don't forget to delete the "-sample" part of the file name once you're done.
Now that you've created your new database and database user (I sure hope you kept copies of the names and password, because you'll need them now), it's time to make some changes to your wp-config.php file. NOTE: when you upload WordPress the name of that file will be wp-config-sample.php. Follow the instructions for making the necessary changes to the file in the "WordPress Famous 5-minute Install" and don't forget to delete the "-sample" part of the file name once you're done.
There are also more detailed instructions for editing the wp-config.php file, but you will likely never need them. If too much information makes your head hurt, I suggest you not even look at the more detailed instructions. I've done LOTS of WordPress installations and never needed to do anything more than what is explained in the 5-minute install.
Before saving your shiny new wp-config.php file, you'll want to do one more thing: change the $table_prefix value. By default the value is "wp_". For some extra protection against hacking attempts, change it to something less generic. You can change the values that come before and/or after the underscore (i.e. "wp_e8x1am4p5le", "e9x_a31pl7e", etc.) Once you've properly configured your wp-config.php file, you're ready to actually install WordPress by heading to https://www.domain.com/wp-admin/install.php - obviously you need to replace "domain" with YOUR domain information, but if you didn't know that already you should stop reading now and never attempt to install or secure a WordPress site yourself. Seriously.
Upon visiting the www.domain.com/wp-admin/install.php URL, you'll be greeted by a WordPress setup page. In WordPress releases prior to 3.0 the "admin" account was created by default during the installation process. Thankfully that's no longer the case. You will be prompted to enter the name of your site, a brief description and - most importantly - the username and password for the initial administrator user account.
You don't have to input your own password. If you don't, WordPress will generate one for you. I don't recommend allowing it to do that. Head back over to Strong Password Generator and create your own password. Remember not to use recommended lengths. Do I really need to remind you of that? I didn't think so. WRITE DOWN OR COPY/PASTE YOUR PASSWORD INTO A FILE! The "New WordPress Site" e-mail will not include your password if you do not allow WordPress to generate one for you.
WordPress Security Plugins
There are several plugins I install on every new WordPress site I build. No single plugin covers all the bases, but combined they offer about as much security for a WordPress installation as is possible.
- WP Security Scan - this plugin will help to bring to your attention some basic security vulnerabilities like the use of auto-generated passwords, file permission issues and the existence of an "admin" user account. Very basic, but very useful. While the information in the plugin directory states the plugin is compatible up to version 2.8.4, I continue to use it on my sites without any problems.
- Secure WordPress - Secure WordPress takes what WP Security Scan began and runs with it. It removes the version information from the site's header, as well as eliminating core, plugin and theme update information for all non-admin users. It also offers an optional free malware and vulnerability scan through sitesecuritymonitor.com.
- Exploit Scanner - it is important to note that this plugin does not actually remove any hacked or suspicious files. That is left for the user to take care of. It can also throw up false positives from time to time, but your site's security is definitely a better safe than sorry proposition. Exploit Scanner notifications are split into 3 categories: severe, warning and note, which helps you to prioritize what needs to be checked NOW and what might be able to wait until you have some free time.
- Limit Login Attempts or Login LockDown - both Limit Login Attempts and Login Lockdown offer similar functionality. Essentially they limit the number of login attempts based on IP address and locks out any IP address that exceeds the limit for a specified period of time. You can configure the number of attempts to length of time of the lock out with each plugin. Limit Login Attempts states it is compatible up to WordPress version 3.0.1 while Login LockDown claims to be compatible up to only version 2.8.4, though I should note that I am still using Login Lockdown on several sites without issue.
- WordPress Firewall - one of the most useful features of this plugin is the ability to have an e-mail sent if there has been a suspected attack. Not only are you alerted via e-mail, but that e-mail includes information about the specific file that was accessed and the IP address of the offender. A particularly noteworthy feature is that when an attack is suspected the offending IP address is redirected either to the site's home page or a 404 page (your choice). You can also whitelist specific IP addresses (like, I don't know - YOURS) so you are still able to make changes to the files associated with your theme or plugins via WordPress without triggering the plugin. Again, the plugin documentation claims the plugin is only compatible up to WordPress version 2.8, but I continue to use it and haven't had any problems with it thus far.
Keep Your WordPress Software Up-To-Date
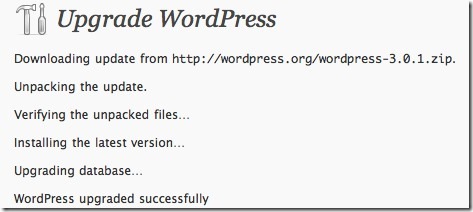
ALWAYS keep your WordPress core software updated to the latest version. While WordPress often makes significant changes to the functionality and usability of the software with major releases, incremental upgrades are often released to plug identified security vulnerabilities and resolve reported issues. You're tempting fate by keeping older versions up & running. You have been warned.
An Added Layer of Security
 Donna Fontenot (a.k.a. "DazzlinDonna" has developed a great tool called "MonitorHackdFiles". It's a cron script that will help to alert you to files that are changed or new files that are added. It won't stop such an attack, but it will alert you via e-mail if it happens so you can immediately take action. Learn more about how to install and use Donna's indispensable tool.
Donna Fontenot (a.k.a. "DazzlinDonna" has developed a great tool called "MonitorHackdFiles". It's a cron script that will help to alert you to files that are changed or new files that are added. It won't stop such an attack, but it will alert you via e-mail if it happens so you can immediately take action. Learn more about how to install and use Donna's indispensable tool.
BACKUP, BACKUP, BACKUP!
 There's no way to secure your site 100%. If you fall victim to a hacker, you damn well better have a backup of your site. Having access to regular backups of your site can not only prevent catastrophe, but make reverting back to a "clean" version of your database quick and virtually incident-free. There are several WordPress plugins available to help you backup your data and protect yourself against data loss in the event of an attack. Here are three you should take a closer look at:
There's no way to secure your site 100%. If you fall victim to a hacker, you damn well better have a backup of your site. Having access to regular backups of your site can not only prevent catastrophe, but make reverting back to a "clean" version of your database quick and virtually incident-free. There are several WordPress plugins available to help you backup your data and protect yourself against data loss in the event of an attack. Here are three you should take a closer look at:
Better Safe Than Sorry
Seem like a lot of effort? Trust me when I tell you that protecting your site is much less time consuming and infuriating than trying to figure out what the hell to do after your site has been attacked. Not to mention the fact that you usually don't even know your site has been hacked until it is kicked out of Google. That is NOT a lesson you want to learn the hard way. BELIEVE ME!
Do everything you can to prevent an attack to begin with any you'll never have to experience first hand what it's like to cross into that whole new realm of monumentally screwed. 🙂